A newly uncovered weakness has shaken confidence in multiple MongoDB versions. It has been dubbed by security analysts as MongoBleed (CVE-2025-14847) and the news has already circulated that attackers are already exploiting it in the field. Over 80,000 servers, which are left exposed to the public internet, could be exposed. Openly published proof-of-concept code and technical advice has been published on how a remote attacker can trigger the bug and steal secret data – passwords, authentication keys and other confidential documents that are never supposed to leave the memory of the system.
The bug has been treated as an urgent issue with a severity rating of 8.7 and the individuals in charge of self-hosted deployments were provided with a patch on December 19, although many systems are still not patched despite the remedy being available.
How a Compression Handling Error Turns Memory Into a Data Leak
The crux of the matter is how MongoDB handles compressed network traffic. Researchers at Ox Security have found that when the server uses zlib to compress data it incorrectly reports the size of the memory buffer it has allocated instead of the size of the data it has actually decompressed. This apparently trivial omission is the precursor of information leakage, as sensitive material held in memory close to the response can be slipped out with the response, almost silently, almost negligently, as though the machine were betraying its content without being aware of it.
By crafting a malformed network request, an intruder can persuade the server to believe that the incoming data, once expanded, is larger than it truly is. The server, trusting this false claim, allocates a generous block of memory and, in the course of responding, may unwittingly hand back fragments of whatever lies within that space.
The material exposed in this fashion can be alarmingly broad: passwords and access keys, cloud credentials, session identifiers, personal data, internal records, settings, filesystem details, even information tied to active clients, all the scraps of a system’s private life.
Why Authentication Offers No Protection Against This Attack
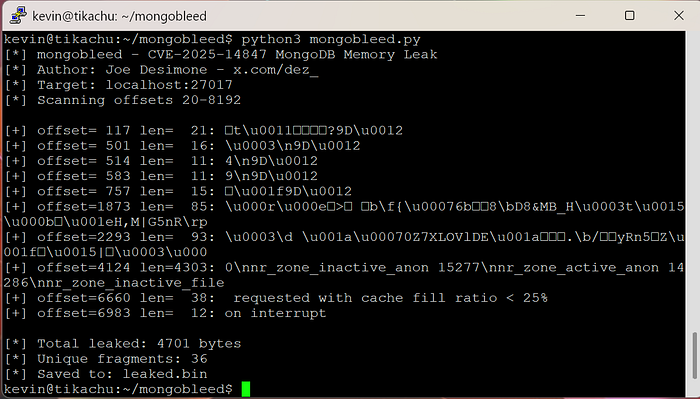
What deepens the danger is that this exchange takes place before any check of identity or permission. No password is required; the door is opened before anyone asks who is knocking. The publicly shared demonstration of this attack, created by Joe Desimone of Elastic, has been built for a single purpose: to draw sensitive information directly from the server’s memory.
Security analyst Kevin Beaumont has reviewed the exploit and confirmed its effectiveness. With nothing more than the address of a vulnerable MongoDB machine on the internet, the tool can rummage through its memory, plucking out database credentials left in plain view, or even secret keys for cloud services.
Tens of Thousands of Publicly Accessible Servers at Risk Worldwide
Data from the Censys search platform paints a troubling picture. As of December 27, more than 87,000 MongoDB servers on the open internet could be susceptible. The greatest number have been found in the United States, with nearly 20,000 exposed, followed by China with close to 17,000, and Germany, which hosts a little fewer than 8,000. Each one stands as a reminder of how easily a system may betray itself when vigilance fades.
Active Exploitation Seen Across Cloud and Enterprise Environments
The scale of the problem in cloud environments seems no less troubling. Telemetry gathered by Wiz, a cloud security firm, suggests that nearly half, 42%, of the systems they could observe run at least one MongoDB instance susceptible to CVE-2025-14847. Their analysts stress that these systems span both private internal deployments and outward-facing machines. Wiz also reports having witnessed active attempts to exploit the flaw, and urges administrators to make patching a matter of immediate importance rather than future convenience.
Rumours now circulate that certain attackers have already used MongoBleed as a stepping stone in a breach involving Ubisoft’s Rainbow Six Siege platform, though such claims remain unconfirmed. Still, the possibility alone has drawn the attention of security practitioners. Eric Capuano, co-founder of Recon InfoSec, cautions that installing the fix is only the first measure. He argues that organisations must also search for traces of intrusion, for what good is mending the door if someone has already slipped inside?
Identifying Suspicious Network Behaviour Linked to MongoBleed
In a recent blog post, the researcher described a practical way to spot suspicious activity: look for a single source sending hundreds or even thousands of connections, yet producing no meaningful metadata at all. It is a simple sign, but one that hints at a machine reaching into places it does not belong. Still, Capuano cautions that such a method reflects only the behaviour of the public proof-of-concept. A determined intruder, he says, could disguise their actions by inserting forged client details or by slowing their pace to avoid drawing notice.
Building on this work, Florian Roth, known for his THOR APT Scanner and vast library of YARA rules, has created what he calls the MongoBleed Detector. The tool examines MongoDB logs with a careful, methodical eye, seeking traces that the vulnerability CVE-2025-14847 has been used against the system. In this way, those responsible for safeguarding their networks may be warned that an unseen hand has already tested the locks.
Official Fixes, Affected Versions, and Safer Compression Alternatives
MongoDB acted on the MongoBleed issue roughly ten days ago, advising administrators to move swiftly to patched releases – 8.2.3, 8.0.17, 7.0.28, 6.0.27, 5.0.32, and 4.4.30 – rather than risk exposure through neglect. The company notes that the flaw stretches across a broad span of past versions, some dating back several years, others introduced only recently.
Vulnerable release ranges include:
- 8.2.0 through 8.2.3
- 8.0.0 through 8.0.16
- 7.0.0 through 7.0.26
- 6.0.0 through 6.0.26
- 5.0.0 through 5.0.31
- 4.4.0 through 4.4.29
- All editions of 4.2
- All editions of 4.0
- All editions of 3.6
Those who rely on MongoDB Atlas, the company’s managed cloud service, have had the remedy applied automatically and need take no further steps. For others, the path forward is more rigid. MongoDB states plainly that there is no true workaround; upgrading is the surest remedy. If that cannot be done, they advise disabling zlib compression and provide instructions for doing so, though this remains a temporary measure at best. For organizations that still require lossless compression, the firm points to safer alternatives like Zstandard (zstd) by Meta, and Snappy, first developed at Google.
Final Words
As MongoDB engineers rushed to seal the leak, thousands of administrators around the globe are now confronted with an unpleasant reality, which is that their databases have been lying on the internet with their proverbial trousers down, happily giving away secrets to anyone who took the time to enquire.
The solution is simple, however, as Eric Capuano rightly points out, it is not much use bolting the stable door when the horses have already run away. Administrators are now detective and have to go through logs to detect any indication of an unwanted visitor who might have already taken their fill of the silverware.